|
Hillridge posted:I'd flatten and reinstall if it didn't take so long to get everything back to the way it was. First you have to install the OS and apply all the updates, which includes what seems like 50 reboots. You can save a little time by slip streaming in the latest service pack to the install disc, but it still sucks. Then you have to reinstall drivers. Then you have to reinstall all the applications and possibly update them. Then you have to reconfigure all the applications and little tweaks you've setup since the last reformat. I'd estimate that it takes me the better part of a week to rebuild my system and get it back to how it was just before infection. Computers are fun
|
|
|
|

|
| # ? Jun 8, 2024 08:34 |
|
Hillridge posted:I'd flatten and reinstall if it didn't take so long to get everything back to the way it was. First you have to install the OS and apply all the updates, which includes what seems like 50 reboots. You can save a little time by slip streaming in the latest service pack to the install disc, but it still sucks. Then you have to reinstall drivers. Then you have to reinstall all the applications and possibly update them. Then you have to reconfigure all the applications and little tweaks you've setup since the last reformat. I'd estimate that it takes me the better part of a week to rebuild my system and get it back to how it was just before infection. Why not make an image next time? Then any subsequent times you could just wipe the drive and put the image back on.
|
|
|
|
BillWh0re posted:Different tools for different jobs mainly. Process Explorer is great for seeing whats happening with loaded modules and handles. GMER is more of a rootkit-revealer type tool and extracts a lot of information about the internal state of the Windows kernel (and even the DOS IVTs and boot sectors). This is pretty much exactly it. ProcEXP doesn't show hidden services or other things like that; this will show (and highlight in red!) the bad guys. It's small and light, but packs a mean punch (insofar as details about what's going on) and is way easy to misuse.
|
|
|
|
ShizCakes posted:ProcEXP doesn't show hidden services or other things like that
|
|
|
|
Reading this thread makes me terrified of the point where they make actual, serious mac viruses.
|
|
|
|
ShizCakes posted:By the way, if you have things that are "hidden", and resurgent or whatever, you need this tool: I've got something that I think is like this. It's just called RootkitRevealer, and I think I got it from the same site I got AutoRuns from. Anyone know which is the better of the two rootkit tools?
|
|
|
|
bazaar apparatus posted:I've got something that I think is like this. It's just called RootkitRevealer, and I think I got it from the same site I got AutoRuns from. Anyone know which is the better of the two rootkit tools? RootkitRevealer is okay, but I think GMER is a more robust version of RootkitRevealer. Not to mention RootkitRevealer hasn't been updated since 2001 I think.
|
|
|
|
What a poo poo day in virus land. We should start posting combofix, malwarebytes, superantispyware, spybotsd, and hijack this logs to use as a community resource. Anyone onboard?
|
|
|
|
abominable fricke posted:What a poo poo day in virus land. We should start posting combofix, malwarebytes, superantispyware, spybotsd, and hijack this logs to use as a community resource. Anyone onboard? And a good word for Dial-A-Fix, which saved me from a repair installation today.
|
|
|
|
abominable fricke posted:What a poo poo day in virus land. We should start posting combofix, malwarebytes, superantispyware, spybotsd, and hijack this logs to use as a community resource. Anyone onboard? On some of these nastier strains of av2009 etc. I've sent myself the log files for research purposes, and I'd be glad to see some other logs if it'd help track some of this stuff down faster.
|
|
|
|
hyperborean posted:If you mean things that hide in svchost or whatever, yes it does. Maybe not to the same extent? And they do have to be running, going by what BillWh0re says maybe they don't with GMER? I use ProcEXP as my task manager replacement on my work laptop, and I don't see the same thing - I've only seen hidden services here and there, but I've never seen one with ProcEXP. I unfortunately lack the terminology to explain what the difference is, but essentially I don't mean the stuff launching as a service through SVCHost (which ProcEXP will show), but services that are actually "hidden" services. There's also some weird process injection stuff that it will pick up and highlight as well - that autoruns doesn't find. It's essentially a robust rootkit revealer, but if said rootkit/hidden process/whatever is in memory, you know about it instantly. Before GMER, I would bang my head against a wall trying to figure out where the hell this poo poo was spawning from. When you get a non-standard PE386 rootkit or some poo poo, you'll understand the true power of GMER. I also like it's ability to kill every process on the system and go into GMER safe mode - without rebooting. Killing auto-regenerating files has never been easier.
|
|
|
|
I think the most inconvenient part is that these days I'm terrified of using any computer besides my own except for menial stuff. It used to be that you could just open the TaskManager and make a judgement call on how clean the computer was. Now, given how well all this poo poo hides, and how easy it is to pick up, the safer bet is to just wait till you get home or use your mobile device if you can.
|
|
|
|
MeramJert posted:Why not make an image next time? Then any subsequent times you could just wipe the drive and put the image back on. I've done this in the past, and unless you make images on a regular basis, it only gets you so far. If you don't store a backlog of images then you run the risk of reverting to an infected one. There's probably a solution for this, but I don't know it. GREAT BOOK OF DICK posted:RootkitRevealer is okay, but I think GMER is a more robust version of RootkitRevealer. Not to mention RootkitRevealer hasn't been updated since 2001 I think. I think SDFix runs GMER as part of its process.
|
|
|
|
Threads like these remind me of the old adage "An ounce of prevention is worth a pound of the cure." Now, I know most people don't intentionally get viruses or malware. I know that some of it is just a flat out pain to avoid, and some things aren't really all that preventable until patches are released. But for the preventable stuff. How do we get the world to be smarter with technology? How do we get idiots to stop clicking on every single loving popup that comes on their screen? I had to fix my step-dad's laptop a few days ago because he just clicks on things without thinking.
|
|
|
|
It's like people forget every bit of common sense when on the internet. If a guy came up to these people on the street (or rang their doorbell) and told them that their house had problems, and they needed his product to fix it, 99% of these people would tell him to gently caress off. On the internet? *click*
|
|
|
|
Hillridge posted:It's like people forget every bit of common sense when on the internet. If a guy came up to these people on the street (or rang their doorbell) and told them that their house had problems, and they needed his product to fix it, 99% of these people would tell him to gently caress off. But SIR! There are *17* spy cameras installed in your house! Including 3 in your bathroom! Also if you don't defragment your waterheater, it will EXPLODE. Pay ME eleventy dollars and I will fix ALL those problems and keep ANYTHING bad from happening again.
|
|
|
|
No sooner does this thread show up, suddenly a friend has popups and bluescreens all over the place. He somehow got Rootkit.TDSSrv, Rootkit.KInject, and Vundo. His slightly wonky hardware isn't helping, either - <1-year old DVD-RAM drive won't boot from 2 different bootable DVDs, handles CDs fine.
|
|
|
|
I just got a good one. Typical "ATTN. WINDOWS MAY BE AT RISK CLICK HERE TO DOWNLAOD (sic) ANTI-VIRUS" popups. Atypical symptoms: whenever I run AdAware or Spybot the computer crashes to a BSOD talking about some "non registered anti-spyware" crap. I'm running a scan in safe mode now to see if that does anything. Another interesting thing, and I have no idea how it can do this, whenever I go to popular AV distributor like Norton or the AdAware/Spybot sites, even malwarebytes.org, I get redirected to some random search page like you see when a domain expires/is squatted. Also there's that lovely new desktop icon labeled "Gay Fetish Sex." Ring any bells, because this one is beyond my (admittedly limited) capabilities.
|
|
|
|
|
I think the computer I am working on today is the worst machine I have ever found. So far antivir has found, I poo poo you not, over 4000 viruses. EDIT: Just for fun 
Capnbigboobies fucked around with this message at 04:30 on Dec 20, 2008 |
|
|
|
Capnbigboobies posted:I think the computer I am working on today is the worst machine I have ever found. So far antivir has found, I poo poo you not, over 4000 viruses. So at what point do you call it a total loss and reformat? 
|
|
|
|
If it was my machine I would nuke the install and reformat. Since it's not my computer I am not going to do that and then reinstall all the bullshit they want, they are not paying me enough for it. Its a dell, but has the recovery partition deleted. I imagine they had some "computer smart" friend check it out a while ago and deleted the backup to have more hard drive space. Yeah buddy real loving smart since they only have a few crappy pictures on the computer and now there is zero way to restore the computer. gently caress it they are not paying me enough for me to bother tracking down my XP home disk to rebuild it. This machine went from so bad you could not do anything, even open my computer or IE to being reasonably snappy. I tried the GMER and it did find a hidden process and I was able to kill and delete it. GMER is pretty cool! It took combofix, malwarebytes, superantispyware, GMER, and antivir to clean it up. Anything else I should throw at it? Ha!
|
|
|
|
GMER is telling me things that the Internet knows nothing about... None of these things show anything in Google, but I think the devices section is fine. GMER 1.0.14.14536 - http://www.gmer.net Rootkit scan 2008-12-20 12:57:18 Windows 5.1.2600 Service Pack 3 ---- System - GMER 1.0.14 ---- SSDT spdz.sys ZwEnumerateKey [0xBA6C6CA2] SSDT spdz.sys ZwEnumerateValueKey [0xBA6C7030] ---- Devices - GMER 1.0.14 ---- Device \FileSystem\Ntfs \Ntfs 8A35D1F8 AttachedDevice \FileSystem\Ntfs \Ntfs SiWinAcc.sys (Windows Accelerator Driver/Silicon Image, Inc.) ---- EOF - GMER 1.0.14 ----
|
|
|
|
Has anyone gotten a virus that seems to block internet connections to specific known anti-virus/anti-spyware sites, and also seems to inhibit such installed programs from actually running? I started noticing pop-ups this morning, so I ran AVG and picked up some stuff, rebooted. I wanted to follow up with Spybot, but now nothing happens when I try to start it up. If I go out and search for it on google, I seem to get redirected to bogus crap now. While I keep my important install executables on hand, reinstalling doesn't seem to help. AVG still seems to be able to scan and pick up threats, but it's not able to connect for updates suddenly. Edit - I'm going to try some of the other tools mentioned. Thankfully I've got my laptop and a thumb drive to get the apps over. Only concern though might be getting the updates. Varkas fucked around with this message at 20:28 on Dec 20, 2008 |
|
|
|
darkforce898 posted:GMER is telling me things that the Internet knows nothing about... None of these things show anything in Google, but I think the devices section is fine. I can't find references to spdz.sys on google (like you said) - find the file on your system and determine if it's related to something of value by inferring from it's location and from it's properties. The SiWinAcc seems to be related to a storage driver - so you should leave it alone. (Silicon Image makes storage controller chipsets)
|
|
|
|
Varkas posted:Has anyone gotten a virus that seems to block internet connections to specific known anti-virus/anti-spyware sites, and also seems to inhibit such installed programs from actually running? Make sure to go to Start->Run->type in msconfig->Startup and google every item in there if you have to, but uncheck the bad ones or any blank spaces. And terminate those processes in Task Manager if you can. And I always go through the registry to get rid of any instances of those items, but you may or may not be comfortable with something like that. Also try booting into Safe Mode w/ Networking and then try going to those sites (superantispyware.com, malwarebytes.org, etc.) and download what you can and rename the executables to something generic like setup.exe, to avoid the installer being blocked by anything. Superantispyware won't install in safe mode but Malwarebytes runs just fine. After I run Malwarebytes in safe mode I generally can reboot back into normal Windows and then run Superantispyware to pick up the rest of the crap. If all else fails, I've never gone wrong with running ComboFix. I believe bleepingcomputer.com has a guide on how to use it. bazaar apparatus fucked around with this message at 20:56 on Dec 20, 2008 |
|
|
|
GruntyThrst posted:I just got a good one. Typical "ATTN. WINDOWS MAY BE AT RISK CLICK HERE TO DOWNLAOD (sic) ANTI-VIRUS" popups. Atypical symptoms: whenever I run AdAware or Spybot the computer crashes to a BSOD talking about some "non registered anti-spyware" crap. I'm running a scan in safe mode now to see if that does anything. Another interesting thing, and I have no idea how it can do this, whenever I go to popular AV distributor like Norton or the AdAware/Spybot sites, even malwarebytes.org, I get redirected to some random search page like you see when a domain expires/is squatted. Also there's that lovely new desktop icon labeled "Gay Fetish Sex." can i see your hosts file please? ( e: A lot of virii do this just to prevent downloading of an AV or updates/etc?
|
|
|
|
ShizCakes posted:I can't find references to spdz.sys on google (like you said) - find the file on your system and determine if it's related to something of value by inferring from it's location and from it's properties. Can't find it anywhere on my computer... Does "search hidden files and folders" search for protected operating system files?
|
|
|
|
Varkas posted:Has anyone gotten a virus that seems to block internet connections to specific known anti-virus/anti-spyware sites, and also seems to inhibit such installed programs from actually running? Sounds like a rootkit, to be honest. The ones I've dealt with in the past wouldn't let me load up any cleaners, and changed some entries in HOSTS that redirected me to other sites when I tried to download fresh copies. I haven't tried it, but give that GMER a try, or RootkitRevealer, see what pops up.
|
|
|
|
Otacon posted:Sounds like a rootkit, to be honest. The ones I've dealt with in the past wouldn't let me load up any cleaners, and changed some entries in HOSTS that redirected me to other sites when I tried to download fresh copies. I haven't tried it, but give that GMER a try, or RootkitRevealer, see what pops up. Thanks for the help guys. I used Avira AntiVir(which interestingly enough wasn't targeted by the rootkit), GMER, and ComboFix primarily to clean everything up. Everything seems to be back to working order now.
|
|
|
|
Varkas posted:Thanks for the help guys. I used Avira AntiVir(which interestingly enough wasn't targeted by the rootkit), GMER, and ComboFix primarily to clean everything up. Everything seems to be back to working order now. It's funny how the arms race doesn't seem to be about the best antivirus anymore, but the one that the virus maker didn't think to block.
|
|
|
|
NotWearingPants posted:
Same with Sophos. It used to catch a bunch of stuff, now, even when it does, it can't remove it. It seems like AV apps go in cycles. Like how Ad-Aware was good for years, then Spybot SD, then (briefly) Windows Defender and now Superantispyware.
|
|
|
|
New techniques for writing malware come out, little unheard-of tools that are the first to jump on them get the praise. The only bit of this that bothers me is when the previously leading antivirus company's response isn't "let's knuckle down and find ways to clean this stuff" but "let's sell out while we're ahead and go all bloaty and shite". I'm waiting to see which way NOD jumps... if it goes the AVG route I may have to switch.
|
|
|
|
HauntedRobot posted:New techniques for writing malware come out, little unheard-of tools that are the first to jump on them get the praise. The only bit of this that bothers me is when the previously leading antivirus company's response isn't "let's knuckle down and find ways to clean this stuff" but "let's sell out while we're ahead and go all bloaty and shite". I'm waiting to see which way NOD jumps... if it goes the AVG route I may have to switch. It almost kind of is going that way, but not in terms of program bloat. I used the latest NOD32 beta from their site and it has the same light memory footprint as version 3. Some new features and so forth. The problem seems to be that ESET is not doing a very good job of keeping up with malware and rootkits. To be fair, NOD32 was designed to be an anti-virus solution more than an anti-malware/rootkit one. However, when you have comparable free solutions like AntiVir and AVG able to handle these types of infections, you can't help but take a look at other software.
|
|
|
|
I picked up that Vundo/Virtomundo and the Antivirus 2009 virus a few weeks ago on my laptop at home and promptly ordered in a flash drive to back up my important stuff before I wipe the machine. I'm going to try to run some of the anti-virus programs mentioned in this thread to see if I can clear it up (defender, vundofix and kasperski either couldn't find it or couldn't remove it). I've got a new desktop coming in tomorrow and after reading these horror stories I'm worried about transferring my documents over from my laptop via flashdrive. Are there any precautions I should take before transferring my files?
|
|
|
|
Yes. Turn off autorun.
|
|
|
|
Autorun should have been disabled with Vista or maybe XP SP2 in my opinion. It seems strange they plugged various holes, but never autorun.
|
|
|
|
Antivirus 2009 isn't that nasty of a virus, it's just that it's everywhere. I've had people at work call me because they visit what looks to be a reliable link off of different search engines and it turns out the page is infected with AV2009. It's not that hard to get rid of if you catch it in time and can remove the System32 files and the registry entries. You just have to catch it before it installs to much other junk.
|
|
|
|
tadashi posted:Antivirus 2009 isn't that nasty of a virus, it's just that it's everywhere. I've had people at work call me because they visit what looks to be a reliable link off of different search engines and it turns out the page is infected with AV2009. It's not that hard to get rid of if you catch it in time and can remove the System32 files and the registry entries. You just have to catch it before it installs to much other junk. Yeah, I all I've ever seen it do is demand money to register it. I don't think it actually mines data or makes spam or anything.
|
|
|
|
Something weird is still going on here. I just did a google search for Scene It: Box Office Smash I clicked the first link, which should be this: http://www.xbox.com/en-US/games/s/sceneitbos Instead it took me to here: http://www.shopica.com/search.php?q=office I hit back and clicked it again and it went to the right site. I did a scan in safemode using malwarebytes a day ago and it found nothing. Should I just throw some more programs at it and see what turns up?
|
|
|
|

|
| # ? Jun 8, 2024 08:34 |
|
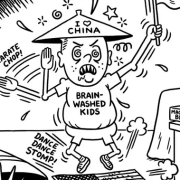
Another tool like GMER is IceSword. It's done by a chinese programmer, but an english version is available. It looks crappy but does an okay job, sometimes some things can hide from gmer but not this, for example
|
|
|