|
TIL that people will pay Cloudflare to add a bunch of nonsense DIVs in their web pages to deter the evil threat of web scraping
|
|
|
|

|
| # ? May 17, 2024 06:37 |
|
Cloudflare's statement: https://blog.cloudflare.com/incident-report-on-memory-leak-caused-by-cloudflare-parser-bug/
|
|
|
|
jre posted:owns owns owns
|
|
|
|
anthonypants posted:Cloudflare's statement: https://blog.cloudflare.com/incident-report-on-memory-leak-caused-by-cloudflare-parser-bug/ quote:We quickly identified the problem and turned off three minor Cloudflare features (email obfuscation, server-side Cusexcludes and Automatic HTTPS Rewrites) that were all using the same HTML parser chain that was causing the leakage.
|
|
|
|
LinYutang posted:TIL that people will pay Cloudflare to add a bunch of nonsense DIVs in their web pages to deter the evil threat of web scraping quote:Many of Cloudflare�s services rely on parsing and modifying HTML pages as they pass through our edge servers. For example, we can insert the Google Analytics tag, safely rewrite http:// links to https://, exclude parts of a page from bad bots, obfuscate email addresses, enable AMP, and more by modifying the HTML of a page.
|
|
|
|
jre posted:Savage
|
|
|
|
Modifying a stream of HTML text: good idea, or great idea?
|
|
|
|
hoowee what a day..
|
|
|
|
Cloudflare has the power to XSS half the internet. Respect.
|
|
|
|
anthonypants posted:Cloudflare's statement: https://blog.cloudflare.com/incident-report-on-memory-leak-caused-by-cloudflare-parser-bug/ While claiming a 3 month average is taking the piss a bit, they are correct that the speed with which they fixed this and deployed to massive infra is impressive.
|
|
|
|
i'm also kind of impressed that they didn't leak any ssl keys, while simultaneously leaking literally everything else
|
|
|
|
somebody has posted a cloudbleed logo in that report. there's someone who is really deserving of a tshirt right now.
|
|
|
|
|
|
|
|
crazysim posted:somebody has posted a cloudbleed logo in that report. there's someone who is really deserving of a wedgie right now.
|
|
|
|
jre posted:Savage
|
|
|
|
anthonypants posted:Cloudflare's statement: https://blog.cloudflare.com/incident-report-on-memory-leak-caused-by-cloudflare-parser-bug/ lol https://bugs.chromium.org/p/project-zero/issues/detail?id=1139 quote:Cloudflare pointed out their bug bounty program, but I noticed it has a top-tier reward of a t-shirt. crazysim posted:somebody has posted a cloudbleed logo in that report. there's someone who is really deserving of a tshirt right now. Proteus Jones fucked around with this message at 00:50 on Feb 24, 2017 |
|
|
|
itym SHAvage
|
|
|
|
jre posted:While claiming a 3 month average is taking the piss a bit, they are correct that the speed with which they fixed this and deployed to massive infra is impressive. Deployment methodologies for these large scale infrastructure services are really impressive. A global kill switch is one thing but being able to deploy a new build to all their edge nodes as quickly and confidently as they do is awesome. Last company I worked at only managed 600 or so and working on the deployment infrastructure was some of the most illuminating work I did. Next job has more like 5 servers total. I don't even know how to work on clusters that small anymore!
|
|
|
|
quick, make a bleedflare logo to compete with cloudbleed
|
|
|
|
Wiggly Wayne DDS posted:itym SHAvage gently caress, outdone 
|
|
|
|
Wiggly Wayne DDS posted:itym SHAvage 
|
|
|
|
Wiggly Wayne DDS posted:itym SHAvage
|
|
|
|
Wiggly Wayne DDS posted:itym SHAvage 
|
|
|
|
just so i'm understanding this properly, the shatter attack requires the collision to be in the first round/block of the file, correct? i've been trying for about an hour to produce a colliding git commit using the colliding block from the PDF, without luck. `shasum` says the files are identical, but `git hash-object` gives different hashes. would this be due to the git header breaking the privileged first-block part of the attack?
|
|
|
|
Angela Merkle Tree posted:just so i'm understanding this properly, the shatter attack requires the collision to be in the first round/block of the file, correct? i've been trying for about an hour to produce a colliding git commit using the colliding block from the PDF, without luck. `shasum` says the files are identical, but `git hash-object` gives different hashes. would this be due to the git header breaking the privileged first-block part of the attack? ya http://alblue.bandlem.com/2011/08/git-tip-of-week-objects.html posted:Git prefixes the object with "blob ", followed by the length (as a human-readable integer), followed by a NUL character, followed by the contents.
|
|
|
|
LinYutang posted:"We've discovered (and purged) cached pages that contain private messages from well-known services, PII from major sites that use cloudflare, and even plaintext API requests from a popular password manager that were sent over https (!!)." i wonder if this is how exmarx doxxed tb
|
|
|
|
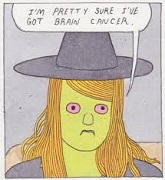
quote:I'm finding private messages from major dating sites, full messages from a well-known chat service, online password manager data, frames from adult video sites, hotel bookings. We're talking full https requests, client IP addresses, full responses, cookies, passwords, keys, data, everything. :rrrrriiippppp:
|
|
|
|
people could have seen my posts
|
|
|
|
Well, since SA is behind buttflare it might be time to change passwords again.
|
|
|
|
https://twitter.com/jcs/status/834922772606308352
|
|
|
|
lol
|
|
|
|
"Terminating TLS is smart and wont blow up in our face!"
|
|
|
|
|
|
|
|
cloumarf
|
|
|
|
somebody post the cloudflare guy's hey taviso stop playing around with desktop av and come work with us and secure the internet tweet
|
|
|
|
https://twitter.com/NathOnSecurity/status/834796736308793344
|
|
|
|
has anyone said cloudfart yet
|
|
|
|
dragon enthusiast posted:has anyone said cloudfart yet buttfart
|
|
|
|
gently caress
|
|
|
|

|
| # ? May 17, 2024 06:37 |
|
PCjr sidecar posted:somebody post the cloudflare guy's hey taviso stop playing around with desktop av and come work with us and secure the internet tweet well i mean i guess he wasn't wrong
|
|
|