|
Wiggly Wayne DDS posted:RWC going well so far That's pretty cool.
|
|
|
|

|
| # ? May 20, 2024 00:36 |
|
apseudonym posted:The bag of certs in a TLS connection is unordered (except that the first one is the server cert), so if you have something like: Thanks for taking the time to explain more. It helped. Wiggly Wayne DDS posted:RWC going well so far This twitter play by play of the talks isn't something I've encountered before. It's neat but since I don't know enough about messaging security I have to resort to the paper.
|
|
|
|
CmdrRiker posted:Thanks for taking the time to explain more. It helped. If you want to know why most attempts to do certificate pinning using Java's standard Trust Management APIs is wrong I can talk about that too
|
|
|
|
apseudonym posted:I have implemented enough trust management that I like to post about it. 
|
|
|
|
on the subject of dumb cert chain poo poo, gently caress s_client the s_client manpage helpfully includes these two options right next to each other quote:-verify depth it's not immediately clear why there are separate options for "set the max chain depth" and "actually fail if you exceed it", but whatever. however, setting both of these and using a chain that's longer than the argument passed to verify does nothing. no fatal error, same output. there is, however, a second block of options, which is just poo poo copied verbatim from openssl verify: quote:-attime, -check_ss_sig, -crl_check, -crl_check_all, -explicit_policy, -extended_crl, -ignore_critical, -inhibit_any, -inhibit_map, -no_alt_chains, -no_check_time, -partial_chain, -policy, -policy_check, -policy_print, -purpose, -suiteB_128, -suiteB_128_only, -suiteB_192, -trusted_first, -use_deltas, -auth_level, -verify_depth, -verify_email, -verify_hostname, -verify_ip, -verify_name, -x509_strict setting verify_depth too short will cause s_client to error out, regardless of whether verify_return_error is present. for extra fun, the depth reported in the output uses a different counter than what's used to determine whether poo poo will fail. output is zero-indexed and includes all certs in the chain: code:code:
|
|
|
|
openssl has too many easily-configured silent error modes and belongs in the trash heap of history since they clearly have zero interest in actually making a usable and secure product for the world but instead are just throwing a loose bag of parts at you with limited constraints or guidance
|
|
|
|
BangersInMyKnickers posted:I 100% assure you the actual mil systems are pushing all their hosed up root and intermediate certs through GPOs to override the numerous PKI validation errors this is true. i have to connect to a lot of sites that follow a chain to root certs that aren't provided by default by any browser or OS. for whatever reason they like their own. also: 
|
|
|
|
i remember back in 2013 when i was still in the navy that you'd have to install a bunch of root certs to make most dod/navy websites functional. it was just a downloadable installer available on a .mil page, iirc. but yeah, without it most mil pages throw up errors and aren't really functional.
|
|
|
|
BangersInMyKnickers posted:openssl has too many easily-configured silent error modes and belongs in the trash heap of history since they clearly have zero interest in actually making a usable and secure product for the world but instead are just throwing a loose bag of parts at you with limited constraints or guidance 
|
|
|
|
BangersInMyKnickers posted:throwing a loose bag of parts at you with limited constraints or guidance that's litterrally the unix philosophy
|
|
|
|
always pay your it staff very well if running a huge drug empirequote:Mexican drug lord El Chapo was only caught because his systems administrator flipped and started working for the feds, backdooring El Chapo's comms infrastructure and providing the cops with the decryption keys needed to eavesdrop on El Chapo's operations. https://gizmodo.com/the-feds-cracked-el-chapos-encrypted-communications-net-1831595734
|
|
|
|
Mr. Nice! posted:i remember back in 2013 when i was still in the navy that you'd have to install a bunch of root certs to make most dod/navy websites functional. it was just a downloadable installer available on a .mil page, iirc. but yeah, without it most mil pages throw up errors and aren't really functional. and even worse, if you install it, most .mil pages don't throw up errors but aren't really functional anyways
|
|
|
|
yeah its cool because so many pages have mixed content where some use certs signed by a root cert that is provided by default but then has embedded assets from pages served with DOD only certs.
|
|
|
|
heh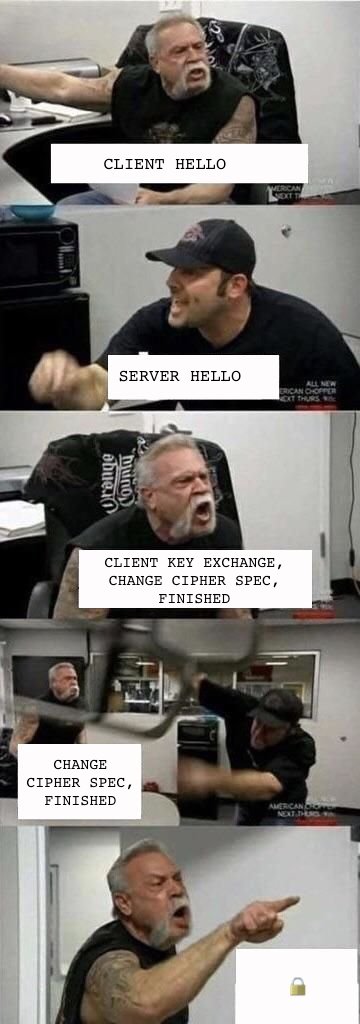
|
|
|
|
apseudonym posted:If you want to know why most attempts to do certificate pinning using Java's standard Trust Management APIs is wrong I can talk about that too I'd like to know about this
|
|
|
|
this online jewellry store i had to buy a family gift from, a decently priced one for the country its located in, not only sent me my initial password, on registration, in plain text, but also the one i changed it to
|
|
|
|
|
UK gov.org revenue and taxes registration page 
|
|
|
|
Jewel posted:UK gov.org revenue and taxes registration page too many characters make it loop back around to not strong
|
|
|
|
Shame Boy posted:too many characters make it loop back around to not strong UNSIGNED_ENTROPY_MAX is a helluva const
|
|
|
|
https://www.qualys.com/2019/01/09/system-down/system-down.txtquote:Qualys Security Advisory
|
|
|
|
"all systemd-based Linux distributions are vulnerable" Ha, that's pretty much every Linux distro I use. Still working my way through the report, though.
|
|
|
|
Some real SOAD fans at Qualys. I haven't heard CUBErt in like 20 years.
|
|
|
|
Vesi posted:I'd like to know about this Alright, posting time. I'm not going to compile the code I write here so if its slightly off Pinning is about protecting yourself from a CA that is trusted by your device but is actually evil, so we assume the attacker owns a CA. For the sake of naming, we've got the follow common certificates: code:The basic naive Java pinning is: code:Ah, so you just need an API to get the actual path from the SSLSession, then its easy! Except Java doesn't give you such an API  . So instead a number of people decided to try and do their own path building before they check pins. I could add a bunch of code here but . So instead a number of people decided to try and do their own path building before they check pins. I could add a bunch of code here but Now, this only works if you always build exactly the same certificate chain as the default TrustManager did, if you ever build a different one there's a problem. That's a terrible idea because a real path building is taking in account things like certificate usage, basic constraints, expiration, etc etc, whereas 'chain cleaners' only build the first possible path based on subject/issuer. In order to bypass this we would need to create a bag of certificates for our evil certificate wherethe real trust manager builds a valid chain to our evil CA but the path returned from the chain cleaner includes our pinned intermediate. With our evil CA this is pretty easy. First we're going to get a valid leaf certificate from CA_g issued by I for a website under our control, call it notevil.com, since CA_g is in the business of issuing leaf certs for websites this is easy. Then we also issue an intermediate CA from CA_b with the same subject and key as our notevil.com leaf certificate and sign Evil with that. The bag of certs we provide is then {Evil, notevil.com_leaf, notevil.com_intermediate, I, CA_g, CA_b}. There are two potential paths in this code:Generally speaking anything that relies on two different implementations of the same spec behaving the exact same way is horribly broken in fun ways, but that's another topic for another post. So you need to do one of: add an API that gives you the chain to make this trivial, write your own X509TrustManager that does pinning checks during chain validation, or figure out how to do it using the JCA APIs which if you can figure out correctly without losing your mind you're a better person than I am. PS: Never pin to leafs and always include a backup SPKI hash if you really want to do pinning. E: Also if you don't follow the cert chains I can make some actual certs as an example, but that's a lot of apseudonym fucked around with this message at 03:33 on Jan 11, 2019 |
|
|
|
Wait, so the validation APIs don't give you any way to tell "hey, here's the trust chain the platform used to determine that this certificate is valid"? Are there any examples from whoever designed that api showing you how it's supposed to be used? Are you just supposed to do 100% of the certificate validation yourself and not rely on the platform doing anything?
|
|
|
|
a miserable bag of certs
|
|
|
|
Jabor posted:Wait, so the validation APIs don't give you any way to tell "hey, here's the trust chain the platform used to determine that this certificate is valid"? Yeah... about that. Realistically you use some extensions/have the OS provide you abstractions so you never have to touch this because also you shouldn't try and write your own X509TrustManager please I beg you let us do it you will do it wrong.
|
|
|
|
apseudonym posted:Yeah... about that. I hope everyone knows that they should never roll their own encryption.
|
|
|
|
Though thinking about it, in common use cases (you're using certificate pinning to ensure you're talking to a server you control), wouldn't it be easy enough to fail validation if the certificate bag contains more certs than you expect? Like, you expect it to contain the leaf cert, your pinned intermediate, and that intermediate's root cert, and absolutely nothing else.
|
|
|
|
Jabor posted:Though thinking about it, in common use cases (you're using certificate pinning to ensure you're talking to a server you control), wouldn't it be easy enough to fail validation if the certificate bag contains more certs than you expect? Good news your CA has changed their infrastructure and the intermediate is now no longer directly issuing certificates but is instead using another intermediate cert in between. SPKI Pinning has lead to far more "welp guess all your clients can't connect anymore sorry pal" than it has prevented evil CA attacks. CmdrRiker posted:I hope everyone knows that they should never roll their own encryption. Might want to check the author of the pinning library I linked apseudonym fucked around with this message at 04:36 on Jan 11, 2019 |
|
|
|
Mustache Ride posted:Some real SOAD fans at Qualys. I haven't heard CUBErt in like 20 years. there's a joke about leaving SSL keys up on a table here but i can't really make it work
|
|
|
|
Shame Boy posted:there's a joke about leaving SSL keys up on a table here but i can't really make it work I don't think you trust in my self signed web certify
|
|
|
|
CmdrRiker posted:I hope everyone knows that they should never roll their own encryption. *rolls d20* critical... 1 
|
|
|
|
E: meh
Carbon dioxide fucked around with this message at 21:44 on Jan 11, 2019 |
|
|
|
because, did you expect anything else? https://twitter.com/doctorow/status/1083444065146789889?s=21
|
|
|
|
effectively free data storage has done absolute wonders for privacy and security lmao
|
|
|
|
jit bull transpile posted:I don't think you trust
|
|
|
|
CmdrRiker posted:I hope everyone knows that they should never roll their own encryption. 
|
|
|
|
jit bull transpile posted:I don't think you trust cry when thinking 'bout PKI
|
|
|
|
geonetix posted:because, did you expect anything else? vehicle 3 has legs
|
|
|
|

|
| # ? May 20, 2024 00:36 |
|
BangersInMyKnickers posted:vehicle 3 has legs the labels are (for some reason) right-aligned to the left of the box they are labeling
|
|
|