|
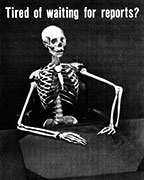
Double the patches, double the security.
|
|
|
|

|
| # ? May 28, 2024 15:14 |
|
2016 has both security only and security & quality, install only one. And wsus maintenance will have an impact on how long your client spends "checking" for updates it won't have any impact on how long it takes to install.
|
|
|
|
guppy posted:There's a LastWriteTime property that might work for you, and you could also filter on PSIsContainer. So something like bless thanks
|
|
|
|
So FIDO2 authentication to Azure AD is in public preview now: https://techcommunity.microsoft.com...DO2/ba-p/746362 Not seeing the option yet in my tenant but I assume it�s rolling out.
|
|
|
|
Is it even possible to work with WSUS in a large environment and know what you're doing?
|
|
|
|
orange sky posted:Is it even possible to work with WSUS in a large environment and know what you're doing? Sorry it's only one or the other.
|
|
|
|
It owns that for the longest time WSUS maintenance best practice was "run these scripts some fuckin dude posted to Spiceworks (and then took down and started charging money for them)"
|
|
|
|
Docjowles posted:and then took down and started charging money for them https://www.ajtek.ca/wam/previous-users-of-adamj-clean-wsus-now-defunct-software/ posted:Please be advised that the use of the early versions of our software known as Adamj Clean-WSUS is now strictly prohibited.
|
|
|
|
Meanwhile, the Mac team at work is having a hell of a time wrangling MSFT's updater for Mac's instance of Office 2016. I'm on the Windows eng side, so I'm probably explaining this poorly, but it seems like the problem is that there's a secondary update engine that downloads the updates and applies them, but it won't indicate that the update is complete until ALL Office products/services are killed and restarted. Which would be fine, but we're under fire for incomplete patching numbers, so those are coming up as false positives. MSFT's advice was to either kill -9 or pkill -SIGHUB (hard kill vs kill gracefully) to force the process to close if the user won't do it on their own. Also, there's a GUI that pops up and requires user input, and the user can cancel said process, and there's no option to either nag them repeatedly or disable the "ignore" button. Also also, if you cache the update, then invoke msupdate again, it downloads the update anyway. And finally, my favorite response from my co-worker: "Curl completely goes around using msupdate. I'm not sure why you would suggest completely going around a supported Microsoft product that was created as a solution for this scenario."
|
|
|
|
nexxai posted:The besterer part of this is that if you visit his website (ajtek.ca), there is this wonderful piece: I pastbin'd the script here and some fuckin goon tattled and had it taken down.
|
|
|
|
lol I remember having to migrate the WID to sql express because we had too many clients/updates and it couldn't handle it, and that was with manual pruning of super-seceded patch sets. I do not miss those days.
|
|
|
|
Dirt Road Junglist posted:Meanwhile, the Mac team at work is having a hell of a time wrangling MSFT's updater for Mac's instance of Office 2016. I'm on the Windows eng side, so I'm probably explaining this poorly, but it seems like the problem is that there's a secondary update engine that downloads the updates and applies them, but it won't indicate that the update is complete until ALL Office products/services are killed and restarted. Which would be fine, but we're under fire for incomplete patching numbers, so those are coming up as false positives. Office on Mac can be distributed through the App Store now, not sure if there's any differences that would cause you problems vs. what comes from MS.
|
|
|
|
Considering the number of times that the build-in office update has managed to deadlock my system somehow, I am very happy to roll the dice on that
|
|
|
|
It's actually funny to me that everyone in the industry agrees that patching is one of the most important activities in IT and there isn't a single really good tool for it. I feel like I should add "relatively easy to use" here
|
|
|
|
Thanks Ants posted:Office on Mac can be distributed through the App Store now, not sure if there's any differences that would cause you problems vs. what comes from MS. We use JAMF to manage patching, so the App Store is, unfortunately, not part of our management strategy.
|
|
|
|
If you're running sccm the wsus database maintenance keeps getting better with every release. If you're running standalone wsus then I just feel bad for you. I ended up with two SUPs (software update points in sccm, backed by wsus) with a shared database for 20k clients and things have been pretty fine. *knock on wood* OH but I once upon a time used an sql express database because Johan said it would be fine and then I hit that 10gb limit and boy was that a fun problem to track down.
|
|
|
|
Thanks Ants posted:Office on Mac can be distributed through the App Store now, not sure if there's any differences that would cause you problems vs. what comes from MS. Oh man, I'm going to try this. Microsoft AutoUpdate on OSX is just a dumpster fire.
|
|
|
|
I've heard that best practice for GPOs is have each GPO only do one thing. If we're going to have lots of things we'll want to do via GPO, what's the best way to avoid having a dozen or two GPOs per OU? Can you nest GPOs like you can security groups so you can apply Policy1, Policy2, etc to SiteA GPO applied to SiteA OU to avoid it becoming a mess, while still being maintainable?
|
|
|
|
H2SO4 posted:Oh man, I'm going to try this. Microsoft AutoUpdate on OSX is just a dumpster fire. Yeah, I think we're about to submit a business justification for a feature request
|
|
|
|
klosterdev posted:I've heard that best practice for GPOs is have each GPO only do one thing. If we're going to have lots of things we'll want to do via GPO, what's the best way to avoid having a dozen or two GPOs per OU? Can you nest GPOs like you can security groups so you can apply Policy1, Policy2, etc to SiteA GPO applied to SiteA OU to avoid it becoming a mess, while still being maintainable? So this is a balancing act. Worth mentioning is a lot of Microsoft "Best Practices" were written 15 to 20 years ago, when slow wan links, slow lan links, and slow computers were the norm. Many of the issues their best practices seek to avoid are overcome easily with today's modern wan/lan links and fast workstations. I don't recall many recent discussions about Group Policy processing slowing down computer logons to the point where users complain. It's just not much of a thing anymore (but it can be if things aren't designed properly). I personally group my GPO's by common settings that apply to a group of people or computers. Depends on how your AD is structured. Our AD is organized by region, and then by site, with sub OU's for Users, Workstations etc. I end up with 3 Site level GPO's for each site OU. For example the Sunnyvale office has 3 standard GPO's, one for users, one for workstations, one for servers. Each one of those GPO's might have 5 to 25 settings in it. What you want to avoid is a huge GPO for everything that has tons of settings and WMI filters and things like that. Try to find a balancing act. Sometimes there isn't one. I have a few one offs in production that were necessary. Still I have over 250 GPO's in production right now. Managing them isn't too bad once you learn how to automate changes to them in powershell. If I need to update 50 site-workstation gpo's, it just takes a minute via powershell. There's no one size fits all when it comes to this. See what works best for you, and feel free to ask specific questions.
|
|
|
|
skipdogg posted:So this is a balancing act. Worth mentioning is a lot of Microsoft "Best Practices" were written 15 to 20 years ago, when slow wan links, slow lan links, and slow computers were the norm. Many of the issues their best practices seek to avoid are overcome easily with today's modern wan/lan links and fast workstations. I don't recall many recent discussions about Group Policy processing slowing down computer logons to the point where users complain. It's just not much of a thing anymore (but it can be if things aren't designed properly). Windows 10 migration is coming up, since we gonna be reimaging most of the computers in our organization, this is a terrific opportunity to automate a lot of stuff we've been doing manually (public desktop shortcuts, software installs, printer mapping, etc) and keep things more standardized as changes happen. I want to make sure that whatever I put together is not only relatively easy to maintain, but understandable by someone who's never seen our AD/GPO structure before. My biggest immediate concern is I don't want to end up with oodles of unsorted policy objects that are difficult to sort through, but also don't want to eventually task someone with digging through all the settings in a policy to figure out what the hell else it seems to be responsible for doing. I really want to learn AD PowerShell, but at least for the immediate future, I'll still need to be able to manage everything via the GUI until I have a better PS understanding and my boss is more comfortable with me using PS for more than queries. Considering that, is there either a good method of documenting and tracking what each GPO does, or quickly displaying everything in a policy that's not default setting? The later would be especially useful, to help me better understand how our prod GPOs are currently set up, as opposed to building what I'd like to do in our test network and hoping for minimal conflict. klosterdev fucked around with this message at 00:13 on Jul 13, 2019 |
|
|
|
I saw the hubub on this over \r\sysadmin and \r\msp a few days ago (due to action pack being discontinued), but Microsoft walked back all the partner IUR cuts they were going to implement.
|
|
|
|
Phone posting but when you look at a gpo in the console it will only show you settings that have been defined. There�s reporting options as well that will give you a list of all the settings that apply to a given computer or user object I�ll post more when I get to a pc
|
|
|
|
As skipdogg said, GPOs will only show settings that have been configured/defined. In other words, settings you've changed. Each GPO should handle one "thing". Have a GPO for creating common desktop shortcuts, or mapping drives, or setting everyone's wallpaper. Within that, you could do some item-level targetings, like users in Accounting get network drive X, while Human Resources has network drive Y. But they should be relatively focused. If there's a lot of settings that need to be changed, it may pay to break it out. For example, at my last role we handled a lot of security hardening through GPOs, to the point where we had three or four "Security" GPOs. GPOS also have a notes/description field that's freeform text. You should write general overview info in there. The Group Policy management tool also has Group Policy Modeling (so you can project what computer and user policies will apply, based on AD OU and site information), and Resultant Set Of Policy (RSOP), which will reach out to the identified computer and user to see what's actually being applied. Modeling and RSOP can conflict in weird and confusing ways, mostly due to read rights as applied to GPOs. RSOP should line up with GPresults run from a client machine. As much as I love PowerShell, I don't think it's a great method for managing GPOs right now, beyond making regular backups. You should absolutely user PowerShell for dealing with AD as a whole, though. Especially if you don't have some third-party tool to handle bulk changes and reporting.
|
|
|
|
GPOs are like building blocks. Build them in the most efficient way for your environment. Bundle them together if it makes sense, separate them if it makes sense. Most importantly, name them in a standardized way and document anything that is not immediately obvious.
|
|
|
|
All of that, and also remember you can build GPOs and test them by only linking them to test OUs, without having to deal with WMI filtering.
|
|
|
|
In all of my years, I have never had to resort to WMI filtering.
|
|
|
|
I mean, I can't remember any good reasons I've filtered by WMI off the top of my head.
|
|
|
|
We have an entirely flat OU structure for users and computers. In our business case with a mostly mobile workforce, we just treat everyone and everything equally with no distinctions when it comes to policy. Any exceptions/targeting is done through security groups, wmi filtering, etc. Policy testing/implementation is easy, I just have a testing sub-ou that I apply my test policy to and move in the appropriate users/computers. If you can get to a flat OU structure, that preps you for jumping to cloud management from a policy perspective, especially once you target via filters. We are implementing autopilot/intune/azureAD with AD P1 licenses for everyone. Since we�re already treating everyone equally policy implementation has been easy. devmd01 fucked around with this message at 13:40 on Jul 13, 2019 |
|
|
|
There are lots of different ways of doing GPOs and most of them have some merit. Your GPO design is mostly defined by your OU layout so if that is already set in stone you have to work within those confines. As someone who does all the group policy for physical and virtual workstations in a megacorp, the best advice I can give you is to leverage the additive nature of group policy. So try to avoid creating 10 base config GPOs for 10 different business units or locations or wherever which are 95% the same. Instead apply the common setting at a higher level or use multiple links. When I came to this place, one change to the common config of everything would mean changing more than 50 GPOs and all the change documentation which goes with an enterprise wide change. Now it�s one edit for most things. As far as separating GPOs into separate functions, it�s not needed in most cases but if it is there is a specific way to do it. Most people get this part wrong. Changes to a GPO trigger reprocessing on other similar function GPOs but this is dictated by Client Side Extensions. Way too much to post here but if you go that route lookup CSE optimization. Also, avoid loop back processing if you don�t hate future you. Enabling loop back processing enables it for every other GPO that computer processes. There are specific additional precedence rules for these. Just don�t and if you have to then spend a good day researching the long term implications so you don�t screw yourself.
|
|
|
|
GreenNight posted:I pastbin'd the script here and some fuckin goon tattled and had it taken down. IT has a lot of libertarians. THE SANCTITY OF THE CONTRACT and anime.
|
|
|
|
We currently have a security expert doing an audit of our network and he's emailed me asking what we use for patch management for Windows and I responded with WSUS. He followed up with:quote:After WSUS applies the patches, how do you apply the registry entries to enable those patches? A lot of the patches aren�t finished until the registries are applied. Can someone tell me what he's referring to? I basically just set up WSUS with auto-approve all essentially and forgot about it.
|
|
|
|
kiwid posted:We currently have a security expert doing an audit of our network and he's emailed me asking what we use for patch management for Windows and I responded with WSUS. He followed up with: Your company is being grifted because this person is an idiot. The only thing that could possibly make sense is if some updates are waiting on reboots or not.
|
|
|
|
Sickening posted:The only thing that could possibly make sense is if some updates are waiting on reboots or not. That's what I responded with. I asked him to clarify since it was my understanding a reboot would typically do this and he responded with this:  He's using Nessus to scan our network.
|
|
|
|
I seem to recall an out of band security hotfix 1-2 years ago that required a registry key to enable/configure. But that is literally the only case I can think of.
|
|
|
|
kiwid posted:That's what I responded with. I asked him to clarify since it was my understanding a reboot would typically do this and he responded with this: Yeah I remember that dumb print thing, and I swear there was a Wannacry/Bluekeep/some big name vuln for a few years back that you needed to install the patch and also enable two registry keys to actually be compliant. Hopefully you are deploying these via GPO and you can just send a screenshot of them over.
|
|
|
|
Sirotan posted:Yeah I remember that dumb print thing, and I swear there was a Wannacry/Bluekeep/some big name vuln for a few years back that you needed to install the patch and also enable two registry keys to actually be compliant. Hopefully you are deploying these via GPO and you can just send a screenshot of them over. No, I wasn't deploying these via GPO. To be honest, I wasn't even aware of it. I'm setting up a GPO to do this now.
|
|
|
|
If you look up the cve, the current kbs don't say anything about needing a registry change.
|
|
|
|
Ugh, Nessus. Any time I get a mention at work about something they found via Nessus, I know I'm in for a massive headache. But lol, our previous CIO thought forced reboots were bad for the user experience! watches patch compliance numbers dwindle
|
|
|
|

|
| # ? May 28, 2024 15:14 |
|
kiwid, I was in the process of writing up a post recommending you use Microsoft Baseline Security Analyzer as a quick/easy/free way to check some of your systems for compliance, but I guess I've been out of the SMB game for too long now, and just learned it's no longer supported. If you also have SCCM in your environment, you could set up some compliance reporting. Otherwise, I use Nessus (sorry, Dirt Road Junglist), there is a free version called OpenVAS that you might be able to check out. I have never used it so this is not a recommendation, just a suggestion.
|
|
|