|
Scrapez posted:This is a voip telephony application running on the ec2 instances and our outbound carrier has to whitelist IPs to allow them to make calls. Based on this; https://docs.aws.amazon.com/cli/latest/reference/ec2/describe-addresses.html Could you apply a filter where association-id is null/empty string? Or pipe the JSON into jq where that attribute is missing?
|
|
|
|

|
| # ? May 21, 2024 16:23 |
|
Cancelbot posted:Based on this; https://docs.aws.amazon.com/cli/latest/reference/ec2/describe-addresses.html This is what I ended up using: aws ec2 describe-addresses --region us-east-2 --query 'Addresses[?AssociationId==null]' | jq -r '.[] | .PublicIp' | head -n 1
|
|
|
|
TAMs are always in Enterprise support since TAMs are only assigned to customers with enterprise-tier support contracts. What office will you be working out of? I�m curious if I�ll be your trainer. And don�t feel bad. I don�t return anyone�s calls. It�s what makes me such an effective TAM.
|
|
|
|
Out of curiosity what kind of support turnaround time from TAMs should we expect? We�ve had some monthly calls with ours and a few people have asked for meetings with various SMEs and have been waiting weeks with no follow up. This has not exactly thrilled our teams and I was wondering if it�s something we should discuss with someone or if it�s usual.
|
|
|
|
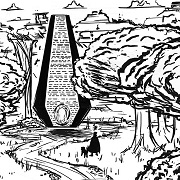
Startyde posted:The first rule of AWS is Amazon hates you I was catching up with the thread, and well:  Thinking of getting it printed.
|
|
|
|
It's beautiful
|
|
|
|
TheCog posted:I was catching up with the thread, and well:  And asking your TAM for a SME should not take three weeks usually. Most importantly, your TAM should not have you wondering what is going on. Pinging your TAM with �uh, we haven�t had an update in a while. What�s up?� is completely warranted any time you are wondering about something.
|
|
|
|
Agrikk posted:What office will you be working out of? I�m curious if I�ll be your trainer. London, or to use what I've head from other AWS people: LHR14. I've been told I'm going to Dublin for a couple of weeks to do the CSE training and then another week of TAM training. There's a new office opening much closer to me but not sure when it's open. For TAM engagement: We had some issues with CodeDeploy and got to a service team within 2 weeks via a joint call with the SA, TAM, and product owner. We got a MS-SQL SME in a week. Cancelbot fucked around with this message at 08:24 on Sep 13, 2019 |
|
|
|
Thanks all, I wanted to make sure it wasn't the norm before bugging people about it.
|
|
|
|
At a previous gig our poor TAMs would get called during practically half our random outages (they were frequent). I think they were our secondary on-call team. But given how much money the company was paying and their visibility they were probably some of their top ones. We had engineer access and got responses usually within hours to get an engineer on the phone (I first wrangled our network guys for dumps and getting cleared with general counsel sometimes depending upon the impact to the corporate network, so it�s not like I used AWS as a surrogate sysadmin team).
|
|
|
|
Cancelbot posted:London, or to use what I've head from other AWS people: LHR14. Holborn Viaduct?
|
|
|
|
Yeah, that's the spot. Couldn't remember the name.
|
|
|
|
I know this question isn't specifically AWS related, but I wasn't really sure where it would fit better. We have an API Gateway that basically fronts a bunch of customer connections to a vendor's service we purchase and offer. We're seeing a average failure rate of around 0.1% (e.g. ~11,000 failures on ~11,000,000 API requests in a month) and since this is the first time I've ever worked on a "real" API, I don't know if that's good, bad, about average, or what. We're well within our contractual rights to our customers (guaranteed 1.5% or less failure rate) but our contracts were written by people who have even less knowledge in this space than I do. I've tried searching for "typical failure rates" or "acceptable failure rates" but nothing really comes up. Is anyone able to give some insight here?
|
|
|
|
Depends on why they're failing, I guess?
|
|
|
|
Jeoh posted:Depends on why they're failing, I guess?
|
|
|
|
nexxai posted:I know this question isn't specifically AWS related, but I wasn't really sure where it would fit better. If its important enough you probably would want a retry or queuing system, but still good to break down the errors and look for patterns like similar types of request, type of error, time of day, amount of requests being sent, if the errors occur grouped together, what the app is doing leading up to the error etc. Then at least if you go to them they might have some insight or you could be finding an issue on their end they aren't aware of. Even if you aren't hitting the SLA they probably would want to avoid it if its a good service.
|
|
|
|
JHVH-1 posted:If its important enough you probably would want a retry or queuing system quote:[...] still good to break down the errors and look for patterns like similar types of request, type of error, time of day, amount of requests being sent, if the errors occur grouped together, what the app is doing leading up to the error etc.
|
|
|
|
You want to Google for availability SLAs (not failure rates). Here are AWS' own SLAs for availability: https://aws.amazon.com/legal/service-level-agreements/. Your availability is currently 99.9% (100 - 0.1), which is not great, not terrible. At AWS, that's where we start paying our customers credits for most services. Your advertised SLA is apparently 98.5% (100 - 1.5), which is pretty terrible. I wouldn't want to use such a service personally. Seems like you could make a stronger promise there.
|
|
|
|
Cross posting from the SQL thread: I have a client that wants to migrate two MSSQL database servers with 200+ db objects between them to AWS Cloud. Now, up until this point we've been fine using Data Migration Service to move the table data from their on-prem servers into AWS EC2 (RDS was ruled out due to cost). The problem is that DMS doesn't migrate indexes, users, privileges, stored procedures, and other database changes not directly related to table data. So now we have generate scripts by hand for these 200+, at minimum, objects. What I'm asking is, is there some hacky way to automate this migration or are we just stuck having to do it all by hand over and over again? Is there some option in DMS to make this happen?
|
|
|
|
Contact your AWS TAM. We've been working intensively with the DMS team and they're really eager to change things based on customer feedback.
|
|
|
|
Jeoh posted:Contact your AWS TAM. We've been working intensively with the DMS team and they're really eager to change things based on customer feedback. drat, really? I�ll have to get ours involved too.
|
|
|
|
Jeoh posted:Contact your AWS TAM. We've been working intensively with the DMS team and they're really eager to change things based on customer feedback. Always this. For every project, you should be engaging your TAM (or entire account team) before you start the project. This way you don�t have to reinvent the wheel ad you�ll be given best practices for your project- ensuring you get it right straight from the beginning.
|
|
|
|
Agrikk posted:Always this. Thanks, this is for a client account. Would there be a TAM assigned even on a basic support plan? SnatchRabbit fucked around with this message at 23:46 on Sep 24, 2019 |
|
|
|
No you gotta pay the big bucks for Enterprise Support to get a TAM.
|
|
|
|
What if you have a Solutions Architect and not a TAM?
|
|
|
|
Internet Explorer posted:What if you have a Solutions Architect and not a TAM? Then reach out to them. Solutions architects exist to help architect solutions. See? A TAM gets assigned to a customer only when the customer signs up for enterprise support (a minimum of $15,000 per year), but technically there is an SA and an Account Manager assigned to every account. That said, territory account managers can have hundreds of customers so access to the SA associated with your account might be limited. YMMV.
|
|
|
|
Agrikk posted:Always this. This is good to know, thanks. Would have helped when doing our migration.
|
|
|
|
Agrikk posted:Then reach out to them. Solutions architects exist to help architect solutions. See? That's basically what I was getting at, the difference between a TAM and an SA for the customer. You got me the info I needed. Thank you.
|
|
|
|
Is there a way to move files into an EFS directly from my desktop machine? Right now, I have to SCP the files up to an EC2 instance and then copy them over to the mounted EFS.
|
|
|
|
This is the only guide I found and requires a VPN between you and your VPC: https://docs.aws.amazon.com/efs/latest/ug/efs-onpremises.html I'm not great with Linux but you could potentially have something to detect & rsync the uploaded/changed files and auto sync that to EFS? It cuts out a step and you might be able to go further and build a rube-goldberg of rsync transactions 
Cancelbot fucked around with this message at 08:32 on Sep 27, 2019 |
|
|
|
Let�s tune Goldberg it up! You could spin up the SFTP to s3 adaptor and then invoke lambdas to move it over to EFS. As to the actual question I�d need to double check but want to say I�ve connected to EFS across VPCs maybe even over a NATed client VPN. Edit: this exists https://aws.amazon.com/datasync/?whats-new-cards.sort-by=item.additionalFields.postDateTime&whats-new-cards.sort-order=desc
|
|
|
|
I did see DataSync. That seems like the method I'll have to go. To expand on my reason for needing this. I've setup our environment in the secure way that AWS suggests with a bastion ec2 host in a public subnet and then all of our ec2 machines in private subnets. The EFS storage is mounted on all the ec2 machines in the private subnets. So, if I want to transfer something up, I have to scp the files to the bastion host and then scp them from there over to the ec2 instance in the private subnets. I don't want to attach the EFS to the bastion as the EFS may contain sensitive data that I wouldn't want accessible from a machine that's in a public subnet. I'll give DataSync a try and see how that does. The crap part is that you have to pay for the service but it does seem very cheap (4 cents per gb of transfer.)
|
|
|
|
Not AWS but hoping someone can help. We have a Varnish server configured to cache requests and behind that we have an Azure load balancer that balances between 3-4 VMs depending on requirements. The problem is that something about the Varnish server being there is causing the load balancer to go stupid and it seems to be confusing the traffic as one visitor and sending it all to the one VM. In other words, it doesn't seem to know or care about the X-Forwarded-For header when determining where to send requests. Am I right in this assumption? Is there any way to configure the load balancer to ignore the client IP and use the X-Forwarded-For header instead?
|
|
|
|
a hot gujju bhabhi posted:Not AWS but hoping someone can help. We have a Varnish server configured to cache requests and behind that we have an Azure load balancer that balances between 3-4 VMs depending on requirements. The problem is that something about the Varnish server being there is causing the load balancer to go stupid and it seems to be confusing the traffic as one visitor and sending it all to the one VM. In other words, it doesn't seem to know or care about the X-Forwarded-For header when determining where to send requests. I don�t know anything about azures load balancer but you might want to see if it could be the load balancer has some stickiness and treats the varnish server as the same user requesting which it would send to the same server.
|
|
|
|
a hot gujju bhabhi posted:Not AWS but hoping someone can help. We have a Varnish server configured to cache requests and behind that we have an Azure load balancer that balances between 3-4 VMs depending on requirements. The problem is that something about the Varnish server being there is causing the load balancer to go stupid and it seems to be confusing the traffic as one visitor and sending it all to the one VM. In other words, it doesn't seem to know or care about the X-Forwarded-For header when determining where to send requests. There are a lot of different ways to load balance traffic but commonly you'll see a load balancer perform some kind of source NAT on incoming traffic, replace the destination IP on it with a selection from its available targets, and then forward it along. The target receives the traffic and perceives it as originating from the load balancer on an IP address level -- almost all of the time this is a good thing. Your target will respond back to the load balancer which usually implements some kind of connection-level tracking and caching and the load balancer does the same thing again: switches the source IP on the traffic to itself, replaces the destination IP, and forwards it back to whoever sent the original request. If you're load balancing traffic like this you actually want the client IP regardless of the X-Forwarded-For header, those headers are usually application specific and outside of some specialized use cases you generally don't want your load balancers inspecting them. If you're seeing your requests through your load balancer not actually being balanced and you've confirmed that you aren't intentionally doing this by setting sticky sessions or similar, you should probably start by answering 2 questions: Are all of your targets healthy, and what algorithm is the load balancer using to balance traffic? It looks like azure load balancers default to a 5-tuple hash based algorithm? The linked page has better documentation but the short version of this is that any time any attribute of your traffic changes, you should get a new backend host. For something like varnish initiating requests to backend servers through a load balancer, each individual request should have a different source port, the source port changing is what should get you a new backend host. You should be able to find out whether or not this is happening pretty easily by tcpdumping from your varnish host and looking at the outbound traffic.
|
|
|
|
OK, I have hit a brick wall with IAM policies and I am looking for help. We are trying to limit access to resources based on application groups. Essentially every application team will have their own groups, one for read-only access and one for read-write. These groups will allow general access to pretty much everything but a few actions (ssm, kms, iam) will be restricted to specific resource paths. Most users will be members of only a single application group but some of our leads will have to be members of multiple groups. In practice this is working perfectly fine for the read-write groups since we've written a policy from scratch that works fine. The problem I'm running into is with the read-only groups. I'm leveraging the AWS-managed ReadOnlyAccess policy which grants List/Describe/Get access to everything and then dropping a another policy on top to restrict access to the resources only allowed in the path. Like this, which will restrict anyone in the group to only have access to read ssm parameters in the /app1 path and prevents a user from decrypting any secrets in the path:code:So my question is how would I go about making these groups work. Do I just split the policy up into smaller pieces? Is there some other way to write a policy that will handle this scenario?
|
|
|
|
Any reason you can�t take the read-write policy, drop the write actions and use that for the read only groups?
|
|
|
|
That�s essentially the solution I came up with. I copied the ReadOnlyAccess policy and broke it up into several pieces to get under the policy size limit. It�s ugly as hell but it works.
|
|
|
|
12 rats tied together posted:There are a lot of different ways to load balance traffic but commonly you'll see a load balancer perform some kind of source NAT on incoming traffic, replace the destination IP on it with a selection from its available targets, and then forward it along. Thanks for the info, super helpful. I looked at the traffic using tcpdump as suggested and it definitely initiates using a different port each time, but always requests port 80 on the LB. Is this a problem? Sorry for the potentially stupid question, I'm far more Dev than Ops unfortunately.
|
|
|
|

|
| # ? May 21, 2024 16:23 |
|
I also don�t know Azure. But from the docs, it seems like what you are trying to do should work fine? Maybe check that you haven�t somehow specified �source IP affinity mode�? Because if each varnish request comes from a different source port, it should be load balancing then across the back ends according to this: https://docs.microsoft.com/en-us/azure/load-balancer/load-balancer-distribution-mode
|
|
|