|
Apparently SAP released a full kernel upgrade which we implemented over the weekend. Fyi if your org has SAP Ed: https://www.cvedetails.com/cve/CVE-2022-22536/
|
|
|
|

|
| # ? May 23, 2024 13:34 |
|
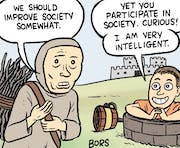
Sickening posted:I really, REALLY doubt that. I am sure they consider it all juicy. There's little reason not to hold that Russia--much like the US and every other country with any meaningful cyber capability--maintains an extensive list of systems / companies / assets that they've managed to get meaningful access into and simply have not decided to do anything with other than sit and monitor and maybe exfil some data. From a practical standpoint, you don't burn every system you get into as soon as you can unless what you're looking for is worth it. So, yeah, there's a reasonable expectation that if things continue to deteriorate, Russia is gonna start leveraging their access to actively interfere with systems where they'd previously just been passively monitoring and maintaining their little beach-head. But yes, regardless of what actually happens, if you can leverage this situation to get your C-suite to finally take security seriously by scaring them with the specter of Russian hacking, then by all means do so.
|
|
|
|
DrDork posted:But yes, regardless of what actually happens, if you can leverage this situation to get your C-suite to finally take security seriously by scaring them with the specter of Russian hacking, then by all means do so. There is a specter haunting your server room -- the specter of
|
|
|
|
DrDork posted:There's little reason not to hold that Russia--much like the US and every other country with any meaningful cyber capability--maintains an extensive list of systems / companies / assets that they've managed to get meaningful access into and simply have not decided to do anything with other than sit and monitor and maybe exfil some data. israel's strat is so much better. give every one of your retired intelligence officers funding for their own "cybersecurity startup", have them all go out and get full read and more permissions on every asset in every environment, then just pick and choose off the menu what you want to poke around in. most of them pay *you*!
|
|
|
|
Gotta maximize those ransomware returns!
|
|
|
|
Are there any security related bulletins one could subscribe to in order to keep abrest of "industry" developments? I'm a product guy running a business unit thats in the process of being audited. Most of our controls are farmed out to corporate but apparently they want us to keep an eye on the going ons of the security industry. Apparently, providing a list of bulletin boards, news groups, sites you read is sufficient for this and I am obviously not going to list something awful dot com on the audit response. I'm in healthcare if it matters but really fishing for any security related stuff. I'd probably read it too since I'm casually interested in the field and lurk this thread for funsys.
|
|
|
|
Do you have any sort of threat intelligence platform you're using? Ive used Anomali Threatstream in the past and really liked it, they included some daily news roundup that was pretty good. Lots of other similar vendors out there as well.
|
|
|
|
Waroduce posted:Are there any security related bulletins one could subscribe to in order to keep abrest of "industry" developments? CISA has a nice mailing list that sends out alerts about vulns and other advisories. Just scroll to the bottom of the page and click Subscribe: https://www.cisa.gov/uscert/
|
|
|
|
yeah CISA is great, I'll dig through my lists and see what I can find.
|
|
|
|
BaseballPCHiker posted:Do you have any sort of threat intelligence platform you're using? Ive used Anomali Threatstream in the past and really liked it, they included some daily news roundup that was pretty good. Lots of other similar vendors out there as well. I dont think we have anything other than whatever comes with basic AWS. I'm not even sure if thats a real answer. Stuff is pretty rudimentary right now. I'm responsible for essentially operationalizing and proceduralizing the SDLC, implementing agile with engineering teams and like level 0 product development stuff if that helps set the background. Not a whole lot of formal stuff going on quite yet.
|
|
|
|
MightyBigMinus posted:israel's strat is so much better. give every one of your retired intelligence officers funding for their own "cybersecurity startup", have them all go out and get full read and more permissions on every asset in every environment, then just pick and choose off the menu what you want to poke around in. most of them pay *you*! Until the chickens come home to roost and there's calls from most parliamentary parties for an official investigation.
|
|
|
|
https://us-cert.cisa.gov/ncas/alerts/aa22-054a Oh joy it has begun
|
|
|
|
SlowBloke posted:https://us-cert.cisa.gov/ncas/alerts/aa22-054a What do you mean? That campaign has been active since 2019.
|
|
|
|
I think CISA alerts are mostly poo poo tbh and almost never contain useful information except for crappy ipv4 addresses and domains for your tier 1 soc people to run through Splunk.
|
|
|
|
Every CISA Alert: APT $StupidName1 changed 3 functions in their existing RAT software therefore we are completely renaming their toolkit as $StupidName2. They are targeting vulnerable $Software with an exploit that has been known for months or longer and a patch has been available for that same amount of time. That exploit is called $StupidName3.
|
|
|
|
We must be on completely different lists then because in the last week I've been alerted to vulns in three different apps that are in our environment. Wouldn't have known about the Zabbix vulns they shared 20 hours ago without it. Their log4j resources were great too.
|
|
|
|
in my experience cisa is a decent warning on current issues without going full nerd while csirt/cert units notification are a "kharak is burning" statement when the smoke clears and the best you can hope for is not being a juicy target so you have time to patch everything up
|
|
|
|
https://twitter.com/1Password/status/1496487659702829061 LOL LMAO
|
|
|
|
goddammit
|
|
|
|
Achmed Jones posted:goddammit Same. Normally I just shrug this poo poo off but now people will be going after 1Password vaults specifically because they could have crypto poo poo in them. Increases the visibility as an attack target in a whole host of ways. gently caress, not sure what to move to.
|
|
|
|
Arivia posted:Same. Normally I just shrug this poo poo off but now people will be going after 1Password vaults specifically because they could have crypto poo poo in them. Increases the visibility as an attack target in a whole host of ways. gently caress, not sure what to move to. Self-hosted bitwarden? KeepassXC & some plain old cloud storage provider?
|
|
|
|
My CISO will never listen to me again. 
|
|
|
|
Rescue Toaster posted:Self-hosted bitwarden? KeepassXC & some plain old cloud storage provider? Yeah, I'm not a fan of rolling my own because I don't trust myself to keep the infrastructure secure (hence paying 1Password all this time), but maybe it's time.
|
|
|
|
Arivia posted:Yeah, I'm not a fan of rolling my own because I don't trust myself to keep the infrastructure secure (hence paying 1Password all this time), but maybe it's time. This is why I like the KeepassXC + cloud storage solution. The password vault and the infrastructure are separated so I can let a cloud provider deal with the storage and sync aspects but still be free to change providers or even roll my own sync solution without having to redo everything else. This also eliminates any concerns about password sync services being high value targets or how much one has to trust such providers on their claims of how much they can access your data. It doesn't work if you need features like shared vaults and such at a corporate level, but for personal passwords it works great.
|
|
|
|
oh come the gently caress on
|
|
|
|
I keep rear end, you should too
|
|
|
|
As if they were even worth keeping after they announced that they were dropping support for standalone licenses/vaults (again).
|
|
|
|
I'm just catching up in the news but some crazy stuff relevant to this thread is popping off with ukraine/russia. Well maybe not crazy but interesting https://twitter.com/ESETresearch/status/1496581903205511181 https://twitter.com/ESETresearch/status/1496614321442459655?t=8pkif924hwxtdMr2133z0Q&s=19 cr0y fucked around with this message at 05:59 on Feb 24, 2022 |
|
|
|
cr0y posted:I'm just catching up in the news but some crazy stuff relevant to this thread is popping off with ukraine/russia. You missed the one where the attackers had taken over the AD server and had the malware pushed to the entire organization via GPO months in advance to be executed all at once 
|
|
|
|
KillHour posted:You missed the one where the attackers had taken over the AD server and had the malware pushed to the entire organization via GPO months in advance to be executed all at once Lockbit2 spreads via GPO. It's the one that hit Vestas late in 2021. Helping them clean up was... stressful.
|
|
|
|
I'm really hoping this Russian war being in the news actually gets me exec buy-in to improve things here. I have a year old credentialed vuln scan thats so full of actual honestly awful red vulns that went ignored for a year. Maybe I actually get a patch policy out of this! Or MFA! I know I'm just getting my hopes up but a man can dream.
|
|
|
|
Arivia posted:Yeah, I'm not a fan of rolling my own because I don't trust myself to keep the infrastructure secure (hence paying 1Password all this time), but maybe it's time.  one-time fee? one-time fee?
|
|
|
|
BaseballPCHiker posted:I'm really hoping this Russian war being in the news actually gets me exec buy-in to improve things here. I have a year old credentialed vuln scan thats so full of actual honestly awful red vulns that went ignored for a year. Maybe I actually get a patch policy out of this! Or MFA! "We hired you to fix it, why haven't you done anything for a year?"
|
|
|
|
F4rt5 posted:BitWarden has cloud vault, and it's either free or a I am an idiot, bitwarden has a guide on their site. Zil fucked around with this message at 17:30 on Feb 24, 2022 |
|
|
|
Thanks Ants posted:"We hired you to fix it, why haven't you done anything for a year?" Its more like "what are we paying all you people for if you just come back with recommendations that cost us money!?!?!".
|
|
|
|
I generally try my best not to interact with other departments at current job, but I was chatting with one of our infosec folks about how we coordinate on vulnerabilities and I just want to make sure I'm not making poo poo up here. Our infosec team currently runs various scanners, keeps an eye on CVEs, etc., but the way they coordinate things needing to be fixed is all over the place. Often times it's a ticket, sometimes it's a conversation in a Teams thread, sometimes it's treated as a project with a spreadsheet. Just the wild west. I described another tool I've used, I believe the concept is called vulnerability lifecycle management, where it's a UI that tracks noted vulnerabilities, infosec can mark them as needing to be fixed, ops team can go in and mark them fixed / won't fix, and then it gets scanned again and confirmed, rinse and repeat. The infosec person had no idea what I was talking about. I'm not going crazy here, right? That is "the right way to do things" and it's called vulnerability lifecycle management, right? If so, what are some of the big names in this space? Internet Explorer fucked around with this message at 23:06 on Feb 24, 2022 |
|
|
|
I remember System Center Service Manager specifically had workflows for this, all the cloud dashboards for whatever the endpoint versions of Defender also have similar functionality
|
|
|
|
@IE sentinel does that(when you bolt in all the defender connectors)
|
|
|
|
Yeah, unfortunately current place is allergic to anything Azure/M365, so I was hoping there was something a little more specific. Something like Tenable, etc. I am going to have a hard time getting them to do anything and it has to be as stand-alone and modular as possible.
|
|
|
|

|
| # ? May 23, 2024 13:34 |
|
Internet Explorer posted:Yeah, unfortunately current place is allergic to anything Azure/M365, so I was hoping there was something a little more specific. Something like Tenable, etc. I am going to have a hard time getting them to do anything and it has to be as stand-alone and modular as possible. Honestly, every org I am a part of just does them as tickets. They find the CVE's impacting devices, platforms, etc, they throw those in a ticket and send it to the person who clicks the buttons to fix them. It takes care of documentation of the problem, who is doing the remediation, and finally the resolution. Its just an simply, repeatable pattern. The big trap is to get stuck in a single tool to look for CVE's. Your org has to be really simple in order for a single tool to do it all. Its usually a big pile of things that you have grab this info from and feed it into your business processes. Sickening fucked around with this message at 23:30 on Feb 24, 2022 |
|
|