|
Volmarias posted:Frankly if you can do anything from the infotainment system, you'll do what the manufacturer could not. I played angry birds on a recent delta flight. It was pretty good, even for a low dpi capacitive touch screen.
|
|
|
|

|
| # ? May 14, 2024 10:43 |
|
Imagine if your job is creating fart apps but for airline entertainment systems
|
|
|
spankmeister posted:Imagine if your job is creating fart apps but for airline entertainment systems Lead ColdFusion Wizard
|
|
|
|
|
spankmeister posted:Imagine if your job is creating fart apps but for airline entertainment systems an ex manager at my old job was a test engineer for airline entertainment systems and he was far and away the worst programmer and manager ive ever met.
|
|
|
|
spankmeister posted:Imagine if your job is creating fart apps but for airline entertainment systems So I popped to the last page after not reading for a bit, and I'm now wondering what the dickens is going on.
|
|
|
|
spankmeister posted:Imagine if your job is creating fart apps but for airline entertainment systems the box itself takes literal years to go from prototype to flight ready and that includes being locked in to specific chips and poo poo not hard to see why there�s a push for wifi
|
|
|
|
https://zwclose.github.io/HP-keylogger/ has this been posted yet? quote:TL;DR: HP had a keylogger in the keyboard driver. The keylogger saved scan codes to a WPP trace. The logging was disabled by default but could be enabled by setting a registry value (UAC required). Get the list of affected hardware and patch here: https://support.hp.com/us-en/document/c05827409
|
|
|
|
Cybernetic Vermin posted:why would you possibly care about this though? the only thing i can come up with where it'd matter on a security level is that it limits the possible aslr entropy, but even that is very minor, making this a hugely irrelevant number on a spec-sheet for almost all purposes 64-bit is the delineation for enforcing kernel driver signing. Maybe they'll shoehorn that in to ARM as well but if they're building it off x86 I doubt it
|
|
|
|
BangersInMyKnickers posted:64-bit is the delineation for enforcing kernel driver signing. Maybe they'll shoehorn that in to ARM as well but if they're building it off x86 I doubt it I thought the limitation on signing enforcement on 32 was compatibility with the billion unsigned 32-bit drivers out there. 64-bit let them set the rules for a new ecosystem, and they could do that on ARM as well. can�t you turn on enforcement on 32-bit, if you have a carefully curated set of drivers?
|
|
|
|
I've never seen a user-controllable way to do it. Maybe somewhere in the guts of the thing the capability is there if you patch the right file though it will probably die when it sees the signing on the module you tampered with is wrong
|
|
|
|
I thought you could do it with a boot flag, but I�m on my phone and the first few pages on Google are all about disabling.
|
|
|
|
I went through all the bcdedit parameters and I don't see anything that looks like it will enable signing for 32-bit https://msdn.microsoft.com/en-us/library/windows/hardware/ff542202(v=vs.85).aspx
|
|
|
|
BangersInMyKnickers posted:64-bit is the delineation for enforcing kernel driver signing. Maybe they'll shoehorn that in to ARM as well but if they're building it off x86 I doubt it ah yeah, this is a good point. as was pointed out above i think this is not the case arm, because at least the old s/rt stuff i am pretty sure had to be all signed, so it'd be weird to drop that. still, this is a solid reason why phasing out x86 does matter a bit
|
|
|
|
Cocoa Crispies posted:the box itself takes literal years to go from prototype to flight ready and that includes being locked in to specific chips and poo poo It is also becoming quite popular to implement in-flight servers as wireless "carry-on" boxes that are just stuck on a shelf and never connected to aircraft systems via any physical cables, thereby avoiding the need for FAA certification. They just swap them out during stops to recharge. However, battery life is an issue - no good to have inflight movies for the first 2 hours of your 10 hour trip!
|
|
|
|
EssOEss posted:It is also becoming quite popular to implement in-flight servers as wireless "carry-on" boxes that are just stuck on a shelf and never connected to aircraft systems via any physical cables, thereby avoiding the need for FAA certification. They just swap them out during stops to recharge. However, battery life is an issue - no good to have inflight movies for the first 2 hours of your 10 hour trip!
|
|
|
|
EssOEss posted:It is also becoming quite popular to implement in-flight servers as wireless "carry-on" boxes that are just stuck on a shelf and never connected to aircraft systems via any physical cables, thereby avoiding the need for FAA certification. They just swap them out during stops to recharge. However, battery life is an issue - no good to have inflight movies for the first 2 hours of your 10 hour trip! Why not just have five of them? Or have two battery slots and have the air crew swap in fresh batteries as necessary?
|
|
|
|
https://www.zerodayinitiative.com/blog/2017/12/13/remote-root-in-directvs-wireless-video-bridge-a-tale-of-rage-and-despair command injection by user-agent string 
|
|
|
|
Also, DV-LINK is at it again https://bgpmon.net/popular-destinations-rerouted-to-russia/ fins fucked around with this message at 17:56 on Dec 13, 2017 |
|
|
|
BangersInMyKnickers posted:I went through all the bcdedit parameters and I don't see anything that looks like it will enable signing for 32-bit It looks like nointegritychecks might do it. https://www.technipages.com/enable-disable-device-driver-signing
|
|
|
|
fins posted:https://www.zerodayinitiative.com/blog/2017/12/13/remote-root-in-directvs-wireless-video-bridge-a-tale-of-rage-and-despair Thanks to the verbose logging on this page I could see that changing my user-agent to "; id; uname -a #" had indeed changed the syntax of the command to be executed. The return value also showed the device had happily executed my new commands and executed them as the root user, too! No login prompt. No input sanitization. Very helpful, verbose output. It literally took 30 seconds of looking at this device to find and verify an unauthenticated remote root command injection vulnerability. It was at this point that I became pretty frustrated. ... 06/14/17 - ZDI disclosed the report to the vendor (security@linksys.com) 09/14/17 - ZDI sent a follow-up to the vendor requesting a status update 10/10/17 - ZDI sent a follow-up to the vendor requesting a status update 11/20/17 - ZDI notified the vendor of the intent to release the 0-day report on 12/12 We have never received any reply.
|
|
|
|
krebs was right! Three Anime Fans Plead Guilty to Creating Mirai
|
|
|
|
Lutha Mahtin posted:krebs was right! anime is a disease
|
|
|
|
Trabisnikof posted:Thanks to the verbose logging on this page I could see that changing my user-agent to "; id; uname -a #" had indeed changed the syntax of the command to be executed. The return value also showed the device had happily executed my new commands and executed them as the root user, too! No login prompt. No input sanitization. Very helpful, verbose output. It literally took 30 seconds of looking at this device to find and verify an unauthenticated remote root command injection vulnerability. It was at this point that I became pretty frustrated. Astounding.
|
|
|
|
https://twitter.com/GCHQ/status/941241855102083073
|
|
|
|
well, seeing how that one in isolation appears to just be ansi terminal escape codes for some, among others, red and yellow text, i'd guess it is going to be stupid but non-nefarious
|
|
|
|
yeah, if you look back at the previous days, it's shaping up to be "print out a colourful christmas tree" or at least, that's what it's going to look like it's done...
|
|
|
|
Lutha Mahtin posted:krebs was right! Verge says Minecraft is to blame: https://www.wired.com/story/mirai-botnet-minecraft-scam-brought-down-the-internet/ edit: ugh... my mind is not working. Wired obv. canis minor fucked around with this message at 17:38 on Dec 14, 2017 |
|
|
|
canis minor posted:Verge says Minecraft is to blame: https://www.wired.com/story/mirai-botnet-minecraft-scam-brought-down-the-internet/ That was a good read. Thanks.
|
|
|
|
there's a good krebs article about it too where he internet detectives some of the authors via their love of some anime character. this was way before any court stuff too https://krebsonsecurity.com/2017/01/who-is-anna-senpai-the-mirai-worm-author/
|
|
|
|
canis minor posted:Verge says Minecraft is to blame: https://www.wired.com/story/mirai-botnet-minecraft-scam-brought-down-the-internet/ Lutha Mahtin posted:there's a good krebs article about it too where he internet detectives some of the authors via their love of some anime character. this was way before any court stuff too Verge article was good. Flashback to Krebs article is always great.
|
|
|
|
Jabor posted:yeah, if you look back at the previous days, it's shaping up to be "print out a colourful christmas tree" the classic Christmas tree attack
|
|
|
|
fins posted:https://www.zerodayinitiative.com/blog/2017/12/13/remote-root-in-directvs-wireless-video-bridge-a-tale-of-rage-and-despair 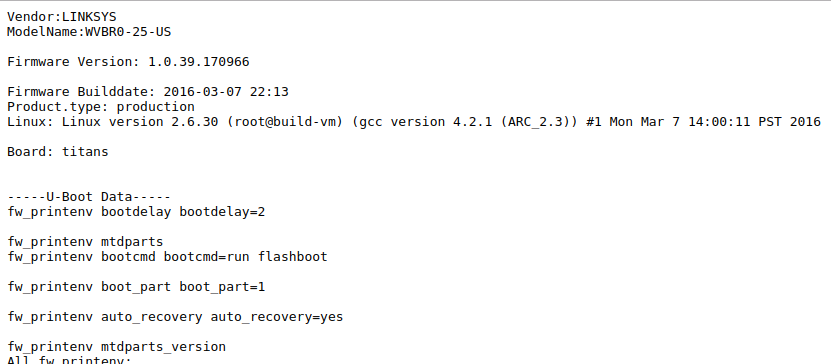 i too wish it was 2009 and not 2017 but alas
|
|
|
|
somebody calling themselves Dr. Cyborkian is claiming they spent the last year operating botnets that bricked everything that could be bricked
|
|
|
|
pseudorandom name posted:somebody calling themselves Dr. Cyborkian is claiming they spent the last year operating botnets that bricked everything that could be bricked Well, he didn't, because I have something very very vulnerable exposed in a terrifying way because of awful business needs. afaik it's still chugging away
|
|
|
|
yeah that's been making the rounds and adds up to events previously seen in the year. notably their reasoning is disabling iot devices that were already being targeted to minimise damage the work in the background of this makes a single person unlikely, but this isn't the first time an anonymous post has appeared from an entity claiming to be a single person with no security background and showing a lot of credible evidence they've done what they've said (e.g. the internet census 2012)
|
|
|
|
poisonpill posted:the classic Christmas tree attack
|
|
|
|
Wiggly Wayne DDS posted:yeah that's been making the rounds and adds up to events previously seen in the year. notably their reasoning is disabling iot devices that were already being targeted to minimise damage
|
|
|
|
anthonypants posted:if something like that were actually happening i would expect to have seen a lot more "hey my iot lightbulbs stopped working after a poc regarding this same model of iot lightbulbs was published"
|
|
|
|
i just realized that at some point i started reading iot as idiot of things
|
|
|
|

|
| # ? May 14, 2024 10:43 |
|
RFC2324 posted:i just realized that at some point i started reading iot as idiot of things Well, you're not necessarily wrong.
|
|
|