|
COACHS SPORT BAR posted:lol holylol
|
|
|
|

|
| # ? May 15, 2024 04:18 |
|
i saw that the petya decryption key was released just the other day practically speaking, how are they obtaining the keys to these ransomwares? i mean, they must be using a crap algorithm in order for this to be possible, right?
|
|
|
|
they did cybers, and countercybers
|
|
|
WAR DOGS OF SOCHI posted:i saw that the petya decryption key was released just the other day sometimes, people reverse engineer the ransomware enough to figure exactly what's happening, and how. this time, similarly to teslacrypt, the author released the private key in public
|
|
|
|
|
cinci zoo sniper posted:sometimes, people reverse engineer the ransomware enough to figure exactly what's happening, and how. this time, similarly to teslacrypt, the author released the private key in public i must be missing something because even if you reverse engineer something that implements something like rsa encryption, you aren't decoding that thing in a few months without the private key -- as you point out, the author would need to release that
|
|
|
WAR DOGS OF SOCHI posted:i must be missing something because even if you reverse engineer something that implements something like rsa encryption, you aren't decoding that thing in a few months without the private key -- as you point out, the author would need to release that
|
|
|
|
|
cinci zoo sniper posted:crypto based on a quadratic function all over 2fa
|
|
|
|
WAR DOGS OF SOCHI posted:i saw that the petya decryption key was released just the other day A few things are in play here: The recent attack on Ukraine was performed using a modified version of Petya, known as NotPetya, ExPetya, Nyetya etc. Modifications included the delivery method (EternalBlue and Powershell/WMI) and a hastily-implemented payment mechanism which didn't work. These modifications were done without having acces to the original source code. I.e. likely not by the original authors of Petya. "Janus" the original author of Petya, contacted Hasherezade, a malware researcher, and gave her the master key for the previous versions of Petya. I.e. the OG ransomware version, not the one used in the attacks. This key cannot be used to decrypt NotPetya. Now, the Petya familiy of ransomware can work in two modes: If it has no administrator privileges it encrypts the files on the machine with the current user credentials using AES. If it _does_ have admin, it will write a new bootloader to the MBR that will encrypt the entire drive using Salsa20. Most recently it became known that certain errors were made in the implementation of said Salsa20 encryption, possibly allowing for the decryption of files. You can read about this recent development here: http://blog.ptsecurity.com/2017/07/recovering-data-from-disk-encrypted-by.html
|
|
|
|
e: nvm
communism bitch fucked around with this message at 19:44 on Jul 10, 2017 |
|
|
|
spankmeister posted:A few things are in play here: you are awesome. thanks for taking the time to post this and for the link!
|
|
|
|
lmao https://thehackerblog.com/the-io-error-taking-control-of-all-io-domains-with-a-targeted-registration/
|
|
|
|
Powerful Two-Hander posted:
i want to know exactly what the "compliance officer" is expected to do in that scenario (i'm sure it's probably just "tell the employee that they are not to give the border guard cash" and "testify under oath that there was in fact a 'compliance officer' available to take the call and 'provide assistance' consistent with the policy blah blah" but i'd love to see that office drone just stammer his way through "uhhhhh well, hmmm...")
|
|
|
|
he's expected to bugger off and let the man handle his bakhsheeshquote:*As an unrelated aside, it�s important to remember to kill tcpdump after you�ve started it. Not doing that is a great way to obliterate your VPS disk space with DNS data, which was an unexpected additional impact of this
|
|
|
|
anthonypants posted:lmao https://thehackerblog.com/the-io-error-taking-control-of-all-io-domains-with-a-targeted-registration/ noice
|
|
|
Mr SuperAwesome posted:noice nioce
|
|
|
|
|
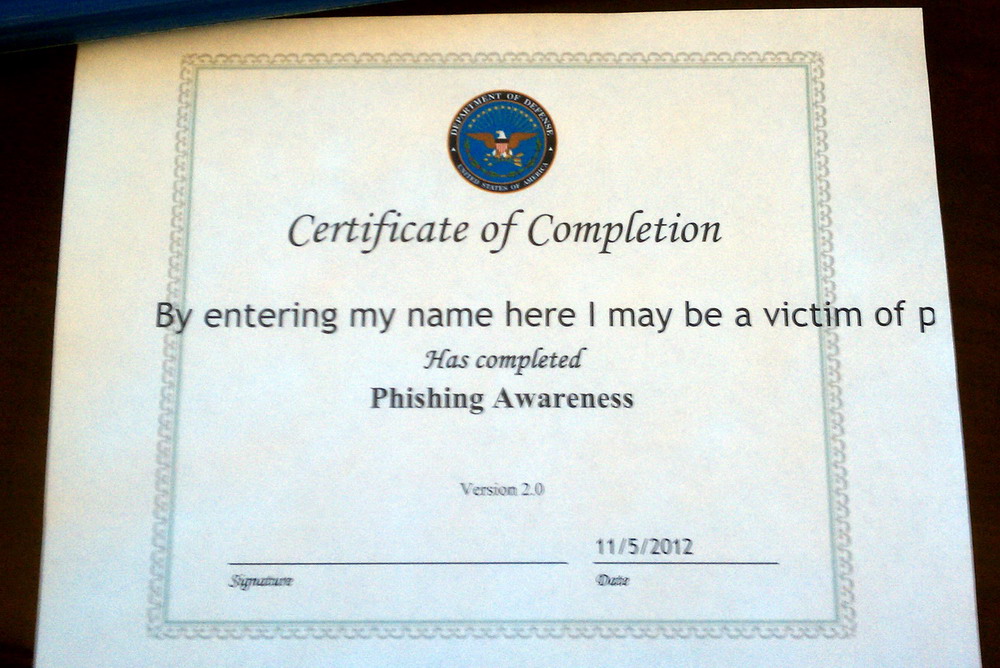
i'm the guy that gets chased by his compliance dept. every year to get all of the tests and quizzes done, and every year I do them at the last possible moment. If any of you work in that capacity I'm really sorry. I'm that guy.
|
|
|
|
im the guy who still hasnt gotten fire safety and electrical safety training
|
|
|
|
|
i used to fast-forward the vids to the end and then answer the obvious questions then they disabled fast-forward for the 18 video segments, so i opened 18 tabs and ran the vids concurrently then they disabled skipping segments before completing the previous one, so now i have to run them in real time in the background as i do real work(sa shitposting).
|
|
|
|
cinci zoo sniper posted:n.io.ce
|
|
|
|
cinci zoo sniper posted:im the guy who still hasnt gotten fire safety and electrical safety training same, but also general work safety training.
|
|
|
Truga posted:same, but also general work safety training. 
|
|
|
|
|
WAR DOGS OF SOCHI posted:i used to fast-forward the vids to the end and then answer the obvious questions usually it's one or two JS variables you can set through the console now that they generally don't use plugins
|
|
|
|
regarding an oracle exploit from the equation group leak https://twitter.com/nicowaisman/status/884507246096519168
|
|
|
|
ratbert90 posted:Hey, these are actually really neat! Do you mind also handling libressl as well? Thanks! Yeah, I will look in to it this week
|
|
|
|
BangersInMyKnickers posted:Yeah, I will look in to it this week Oh I've been meaning to ask you why you chose the ecc curve order that you did.
|
|
|
|
spankmeister posted:Oh I've been meaning to ask you why you chose the ecc curve order that you did. 
|
|
|
|
for all mandatory trainings, the procedure is: find a browser where the training works, then just skip skip skip immediately to the end and start masterminding the quiz: "okay, a a a a a a a a is 35.7% correct, how about b b b b b b b b..."
|
|
|
|
maskenfreiheit posted:instead of facebook try face to face book error: no results found for face showing results for feet instead
|
|
|
|
https://twitter.com/hackingdave/status/883895580749160449
|
|
|
|
He registered a company in that name to get the code signing cert lmfao
|
|
|
|
To be honest, real companies don't have that much better names. TrustedSec, LLC. sounds just as stupidly real as tons of other real companies.
|
|
|
|
spankmeister posted:He registered a company in that name to get the code signing cert lmfao In the past, the title field wasn't signed so you could put whatever in there and it would show it. This one guy made a demo of this to point out how poo poo it was and noticed in his web server logs two people from Oracle had tried it with titles such as "who gives a poo poo"
|
|
|
|
reminds me of like 15 years ago and using IE and getting sketchy activex controls with long names saying they're totally cool and safe and begging to be installed
|
|
|
|
spankmeister posted:Oh I've been meaning to ask you why you chose the ecc curve order that you did. Anything in particular? I lean to the NIST curves over Brainpool because I feel they are more heavily vetted (and I am a CIA plant). 25519 is young but under a lot of review, with a strength roughly equivalent to P256 so it goes in the middle.
|
|
|
|
spankmeister posted:He registered a company in that name to get the code signing cert lmfao not unlike being 15 and using the AOL screen name BillingDept to phish people
|
|
|
|
if we use asas is there a good alternative to anyconnect or should we be using anyconnect
|
|
|
|
LibreSSL 2.5.4 configcode:
|
|
|
|
anthonypants posted:if we use asas is there a good alternative to anyconnect or should we be using anyconnect i'm wondering this too, because i bought a couple grey market ASAs for personal use and i'm not sure how the vpn stuff will shake out i found this: http://www.infradead.org/openconnect/ might be useful?
|
|
|
|
BangersInMyKnickers posted:Anything in particular? I lean to the NIST curves over Brainpool because I feel they are more heavily vetted (and I am a CIA plant). 25519 is young but under a lot of review, with a strength roughly equivalent to P256 so it goes in the middle. Thanks. Nothing in particular, just wanted to know your reasoning. Some of the curves are unsafe according to djb et al: https://safecurves.cr.yp.to/ But I don't know enough about ecc to really understand the implications of "unsafe" curves.
|
|
|
|

|
| # ? May 15, 2024 04:18 |
|
RISCy Business posted:i'm wondering this too, because i bought a couple grey market ASAs for personal use and i'm not sure how the vpn stuff will shake out e: nevermind, i found the windows installers
|
|
|






















 . Please note that any DNS data recorded for debugging purposes has now been purged for the privacy of the users of the .io TLD/its domains.
. Please note that any DNS data recorded for debugging purposes has now been purged for the privacy of the users of the .io TLD/its domains.